It seems that hackers are deploying increasingly sophisticated malware to target cryptocurrency owners. In the last couple of days, a phishing scam that tricks Ledger Live users into revealing their wallet seed, as well as an NSA-developed “cryptojacking” virus targeting Asian companies, were revealed.
Ledger Live Attack
Ledger announced a few days ago that they had detected a phishing attack on their Ledger Live desktop application.
This type of malware is called a phishing attack and is very common in hacking attacks on e-commerce companies and users, bagging millions, if not billions, of dollars, each year.
Ledger Live Malware – how does it work?
With more details slowly emerging, it appears that the following modus operandi is used:
Step 1: Users’ computer security is compromised (it’s unknown exactly how at present.)
Step 2: Malicious malware is implemented that replaces the official Ledger Live desktop app with a tampered-with version.
Step 3: The compromised app claims that the user’s Ledger needs to be restored and therefore the user should provide the desktop app with their 24-word seed.
Step 4: When a user complies and enters their unique seed, they give the hacker access and the ability to steal their whole investment within minutes.
Ledger Malware affects only desktop users

Ledger has been quite proactive and transparent in handling this security issue, which at present seems to affect only a small number of its Windows desktop users, but it’s still a worrying problem nonetheless.
Their tweets links to an older article that states that users should only reveal their 24-word phrases if they want to either 1) clone a current hardware wallet or 2) have lost their old wallet and need to activate a new one.
While the French-based leading hardware wallet company assured their users that the phishing software did not originate from Ledger, nor did it affect the app’s intrinsic security or functionality, the problem remains that this malware can easily dupe inexperienced or distracted users into revealing their private data, as it looks so authentic.
Ledger is correct when they say that user education is most important to combat this. And this problem won’t go away soon either.
As long as a computer connects to the internet, it will always be susceptible to hackers who will exploit vulnerabilities and user ignorance to implement malicious software such as phishing scams and keyboard loggers.
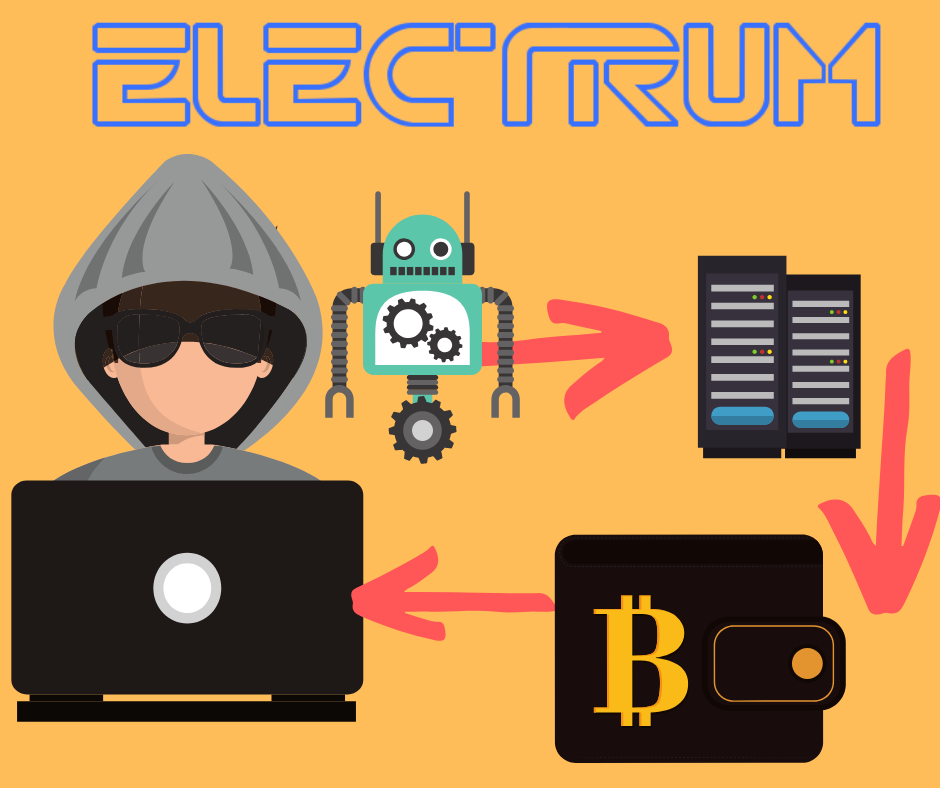
These scams have a long history of finding their marks when targeting cryptocurrency wallets, most notably a very recent DoS phishing attack on desktop wallet Electrum that netted millions.
It doesn’t help either that these malware programs are often developed by governmental security agencies such as the … NSA.
New NSA-created Malware targeting companies
Yes, that’s right. The reason why so many of these viruses are so sophisticated is because they’re utilizing hacking tools that were developed by governmental security bodies such as the US’ National Security Agency (NSA).

Only 2 days ago, Symantec released a report which claimed that a new malicious crypto-jacking program called “Beapy” was detected.
The virus sends out infected Excel spreadsheets to users. Once company employees open them, the virus then spreads through a company’s whole computer network, using the dreaded “Double Pulsar” malware which was developed by the NSA, stolen and re-released as a virus, most notably during the infamous WannaCry ransomware attacks of 2017, where users were unable to unlock their machines without paying money to the hackers.
Once DoublePulsar is installed on to a user’s computer, it downloads a Monero “miner” application while it uses another leaked NSA tool, EternalBlue, to spread across the compromised network through unsecured computers where it can grab more credentials to further access patched machines.
Is a mobile app safer than a desktop app?
In general, yes. There a number of reasons for a mobile environment is relatively much safer and more controllable. Here are a few:
- Mobile apps are usually available from official stores for Android and iOS devices. In order to be listed, they need to be verified and tested for malicious code, which makes it highly unlikely a malware-infected app will be added.
- Most viruses target Windows desktop computers through infected websites and browsers, as mobile devices are more difficult to breach due to different operating systems, devices and usage.
How does CoolWallet keep users safe from phishing attacks?
CoolBitX are Fintech security experts who enjoy the support of our EVM-certified parent company SmartDisplayer,a Visa and MasterCard partner. Online security weaknesses and poor portability were some of the biggest reasons we why gave desktop computers a wide berth when we first developed the CoolWallet S.
We therefore made a conscious decision to build our hardware wallet to work exclusively with a smartphone and thus limit the risk of phishing attacks.
(Or maybe it was just because guys like John McAfee pioneered the first anti-virus internet solutions – much as we love colorful personalities like you John!)

Our CoolWallet app for the CoolWallet S is only available on the official iOS and Android stores. Users can ensure their safety by only downloading and installing our trusted app from these official sources. Please avoid dowloading from unauthorized sources.
While your funds will remain safe as our Secure Element will reject and not sign any fraudulent transactions, malicious parties could trick you into revealing your 12-24 phrase recovery seed.
Please note, CoolWallet and CoolBitX will NEVER ask you for your private seed recovery phrase. By disclosing it to anyone, you risk losing all your funds.
If you have any questions on the topic, please go to our Support page.



