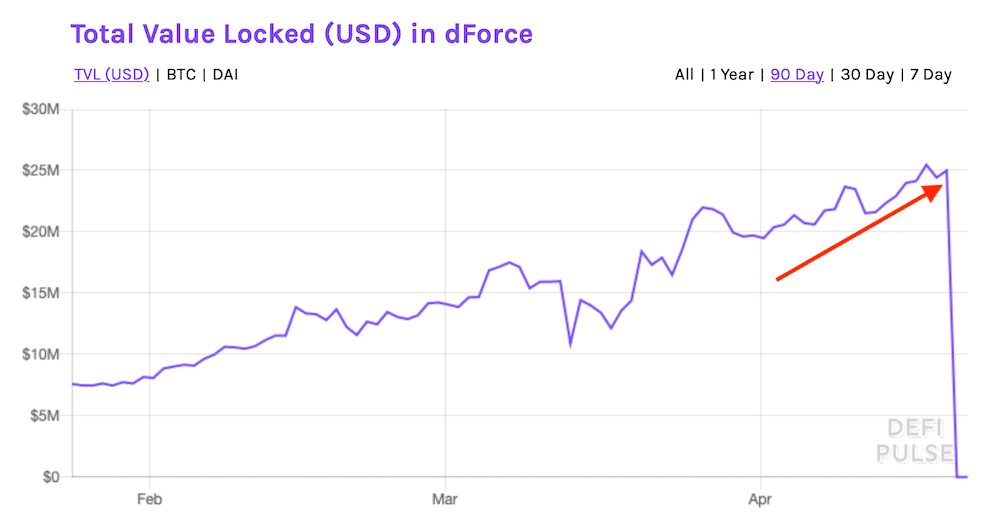
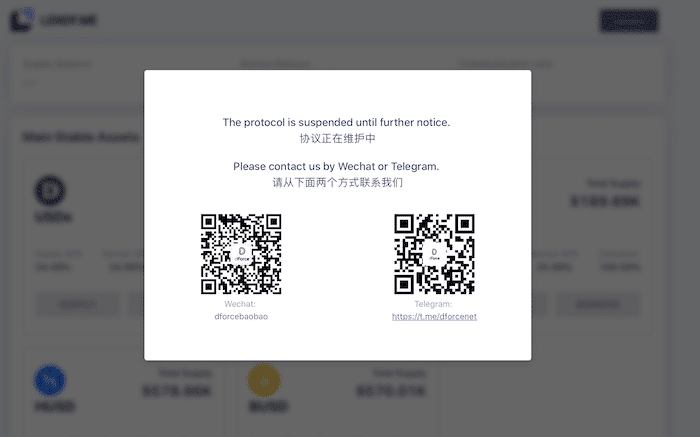
It looks like the DeFi community took another hit recently. Lendf.me, a part of the dForce network, had over 99% of its assets drained on the morning of April 19, 2020. Estimated losses of around $25 million in Ether (ETH) and Bitcoin (BTC) have been reported. Unlike other hacks in the past, it seems that the attacker is now negotiating terms with the founders of Lendf.me.
How was Lendf.me hacked?
The hacker used the imBTC token as a Trojan to implement the attack. imBTC is an Ethereum wrapper for Bitcoin. It is an ERC-777 token that is pegged on a one-to-one ratio with Bitcoin. In this attack, it was used as collateral to take advantage of an exploit in Lendf.me’s contract that handles user balance updates.
How the attack works is quite simple. The hacker deposits some imBTC into Lendf.me which quickly registers into his account’s balance. They would then make another small imBTC deposit within the same transaction which would trigger a “reentrancy”. This trigger automatically withdraws the initial deposit of imBTC. After the withdrawal, the contract fails to update the user’s balance which allows for them to deposit the imBTC again. This lets them effectively double their balance with each transaction. The hacker eventually drained almost all of the imBTC available on Lendf.me. The fake imBTC balance was then used to borrow all the other tokens available on Lendf.me.
Lendf.me hacker almost caught
After the attack, the hacker sent PAX tokens worth up to $250,000 to 1inch.exchange, Paraswap and an account called “Lendf.me admin”. They then returned about $2.6 million worth of assets back to Lendf.me which some have interpreted as a peace offering. The owners of Lendf.me have since responded with the message, “Contact us, for your better future”.
Other small details of the hacker’s location and identity have also been revealed. The transactions made to 1inch.exchange came from an IP address located in China. However, it is possible that a VPN was used to avoid being caught. Some details about their computer info has also been discovered. These details include their screen resolution, system language (en-us) and that they are using Mac OS. Although this kind of information will mostly likely not bring them any closer to catching the hacker, it does prove that they were not completely stringent on covering their tracks. The CEO of 1inch.exchange adds, “He seems to be a good programmer, but an inexperienced hacker.”
Keep your crypto off exchanges
To avoid losing your precious tokens from these types of attack, the only solution would be to keep your crypto in cold storage. The most secure way would be to store your private keys in a hardware wallet. With the CoolWallet S, transferring your cryptocurrency from the wallet to an exchange can be done anywhere, anytime, thanks to the convenience of its smartphone app. With our hardware wallet, your funds are safe from exchange hacks and exploits.

No matter how safe and secure some exchanges claim to be, bad actors will almost always find a way to exploit the system. The only thing you can do is make sure that your crypto is in a place where they cannot access. Let’s just hope that this hacker in particular will get caught and eventually return all of the stolen assets.
Updated 4/22/2020: Hacker returns almost all stolen assets from dForce
Great news! It looks like the hacker has returned a good portion of the stolen assets. Assets were returned in ETH, WBTC, HBTC, imBTC and other various stablecoins. Up to $24 million was returned, which is about a million short of what was stolen. Reasons for why the funds were returned or why it wasn’t the full value is yet to be determined.



