This week, many Binance users who own Litecoin (LTC) fell “victim” to the first Litecoin dusting attack, when they received a miniscule amount of LTC (0,00000546 LTC) from an unknown source. A similar incident happened to Bitcoin owners in 2018.
So how is free crypto from strangers a bad thing? What is a dusting attack and how serious a threat is it? Why do dusting attacks happen, who is behind them and how can you avoid them? In this article, we’ll answer these questions and more.
Table of Contents
- Overview: Litecoin dust attack
- What is dusting?
- What is the purpose of dusting?
- How do you stop dusting?
- How does dusting affect CoolWallet S?
Litecoin dusting attack on Binance
The attack happened across the whole network and all Binance users with active Litecoin addresses at that time were affected.
Binance quickly pinpointed the culprit as someone who owned this Litecoin address, which was later revealed to be a Russian mining pool company who wanted to advertise their services to Litecoin users in a marketing ploy that badly misfired.
“The person behind the dusting attack owns a mining pool based out of Russia. They reached out to express that their intent was to advertise their mining pool to the users of Litecoin, however, it’s unclear from our perspective or anyone else’s as to whether there were alternative motives. The owner of the pool was not aware that he was subjecting all these users to a dusting attack and spreading fear among the Litecoin community.
James Jagger, Binance Academy head, in an interview with CoinTelegraph
While Binance initially said only 500 users were affected, it is now estimated by a third-party analyst that over 300,000 accounts were “dusted”.
2018’s Bitcoin dust attack
The same thing happened in late 2018, when thousands of Bitcoin wallet owners found they received 888 Satoshi from an unknown entity.
It was later revealed that BestMixer, a crypto mixer company, was behind this, in a mass advertising campaign that worked out more cost-effective and PR-boosting than using Google Adwords. Media sites immediately labeled this a new form of spam, while blockchain transaction AML trackers such as CipherTrace raised their concerns on the dusting attackers’ true intentions.
What is a Crypto “Dusting Attack’?
A crypto dust attack happens when an unidentified malicious party (scammer or hacker) sends a miniscule amount of crypto (usually Bitcoin or the big altcoins) to thousands of different public crypto addresses in order to reveal the real identity of the address owners.
Bitcoin owners, for example, might receive a staggering 1 Satoshi, which equates to 0,000000001 BTC, without them even knowing it, as “dust”, a tiny amount of crypto often accumulating in cleared out accounts, is usually automatically hidden by exchanges in order to make your asset portfolio look less cluttered.
Binance Academy made this excellent explainer video last year on dusting attacks:
Dusting is all about output. UTXO, that is.
Without going into too much technical detail, the core of a dusting attack constitutes a cryptographic element found in virtual assets like Bitcoin and Litecoin, called the unspent transaction output (UTXO).
A UTXO defines a blockchain transaction output that has not been spent, that is, used as an input in a new transaction.
It is essentially a signature attached to an unspent value that merges with other UTXO’s when a transaction is executed. A hacker or scammer can track wallets and connect them to one user just by monitoring these UTXOs . If you want to know more, here’s a comprehensive guide on UTXO.
Is “dusting” a serious security threat?
While dusting is not as direct and immediate a threat as other crypto scams and hacks, it raises several red flags for affected users because your identity can be compromised. This makes you a target for bad actors who can either try to scam or hack you or use extortion through blackmail.
What is the purpose of a “dusting attack”?
A dusting attack is very different from other hacks and scams such as phishing, cryptojacking (hijacking your PC to mine crypto), ransomware and other nefarious tactics.
Most hacks and scams revolve around stealing your cryptocurrency investment or your computing power in order to mine new assets.
Simply put, crypto dusting aims to steal your anonymity. The attacker(s) wants to link your different accounts together so that they can figure out who the person is and what assets they own. There could be a number of reasons for this, such as:
1. It’s the groundwork for a phishing or extortion attempt
By figuring out which addresses are related, scammers can connect the dots and uncover the shared identity behind all your different crypto addresses.
Once they have figured out who you are, this puts you directly in their crosshairs. They can then “mark” you as a potential phishing target if you have enough high-value assets (as determined by exploring the public blockchain records on tools such as blockchain.com.) To learn more about phishing schemes, check out our guide on how to stop phishing attacks.
2. It’s the government snooping around or getting fooled
So you spread your Bitcoin over 100 addresses to fool Uncle Sam for tax purposes, libertarian ideals or darknet purchases? Not so quick.
Crypto such as Bitcoin and Litecoin are not purely anonymous virtual currencies, they’re pseudonymous by nature. That means that while your real-world identity is not revealed, your transactions, wallet size and other information is there for anyone to peruse on the blockchain.
Digital exchanges and some wallet providers have made Know-Your-Customer (KYC) registration a standard procedure now.
Moreover, in order to combat money laundering and terrorism funding, Anti-Money-Laundering (AML) watchdogs such as the Financial Action Task Force (FATF) and the Financial Crimes Enforcement Network (FinCEN) are now making the regulation of cryptocurrencies a priority.
The Travel Rule for crypto
They want to ascertain the real-world identity of virtual asset owners and the purpose of transactions. To achieve this, they’re using the “Travel Rule”, first introduced in the U.S.’ Bank Secrecy Act (BSA) for traditional banking.
The Travel Rule has now been adopted by FATF and puts pressure on countries to regulate their virtual asset service providers (VASPs). VASPs like digital exchanges must now share both originator and beneficiary information, similar to how traditional banks use SWIFT codes.
Dusting can be an excellent tool for authorities to see who’s hiding what crypto where. Think of dust as akin to exploding purple dye used by banks in their cash bags to discourage robberies.
Example: Dusting is a great tool for the FBI to track certain accounts likely involved and follow the money trail. Indeed, it’s no coincidence that FinCEN’s unofficial slogan is indeed “Follow the money”.
On the other hand though, dusting can also be used to sabotage AML operations. By contaminating thousands of wallets, criminals can lead regulators on a wild goose chase, making it impossible to track funds.
So for example, while the BestMixer Bitcoin dusting marketing campaign seemed harmless, they “infected” thousands of wallets with “mixer” crypto. This possibly puts these wallet owners on the radar of AML agencies.
3. It’s a cheap marketing gimmick (or is it really?)
Can a dusting attack ever be completely innocuous, mere flecks of crypto goodwill laced with wealth-sharing intentions?
Yes, if you believe the Russian mining pool owner behind the Litecoin dusting fracas.

They were not the first to do it either. Last year, publishing platform Steemit did the same, dusting user accounts with a tiny amount of free Steem Dollars (SBD).
James Jagger, Binance Academy project lead and whistleblower on the Litecoin dusting attack, elaborated more in a CoinTelegraph interview:
“Even if this wasn’t the intent of the mining pool owner, he provided a base for malicious actors to analyze. You see, the person responsible for conducting the dusting attack doesn’t necessarily have to be the one collecting the data. They can merely be providing a service so that someone else can collect and analyze all the information later.”
How can you stop a “dusting attack”?
In short, to negate an attack, don’t spend the received dust, and mark it as “Do Not Spend” if possible.
As Samourai Wallet advised in 2018:
You can also create additional wallet addresses for new transactions. Lastly, if this is still a major concern for you, you can also use obfuscating technology like a Virtual Private Network (VPN) to hide your tracks.
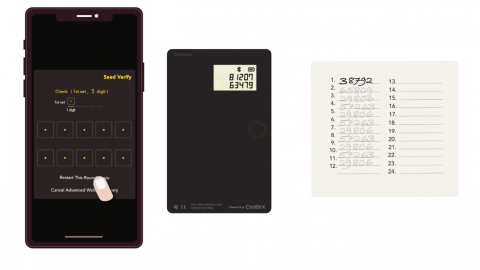
How can CoolWallet S users avoid dusting attacks?
In short, you can’t. You cannot stop anyone from sending crypto to your address. This doesn’t mean that the dust has to be harmful to you though.
CoolWallet S is a hierarchical deterministic (HD) wallet which is designed to offer better anonymity to users. An HD wallet creates a different public address during each transaction so that the owner’s identity remains private. This is directly in line with what Satoshi Nakamoto’ s Bitcoin whitepaper recommends.
If you worry about dusting and anonymity and security issues it can saddle you with, then the solution is simple:
Don’t combine different wallet addresses together in one transaction.
For example, you have three BTC wallet addresses on your CoolWallet S, each containing 1 BTC (for a total of 3 BTC) and you want to transfer 2.5 BTC in a transaction. To stay safe, it’s best to transfer the 2.5 BTC into 3 separate transactions ( 1+1+0.5BTC), not one. This way, your addresses don’t end up in one TX block.
Conclusion
While dusting attacks are not as serious or pressing a security issue as other attacks, it is still an attack that is meant to take something from you by giving you something else for free.
An often-quoted economic principle is that “there ain’t no such thing as a free lunch” (TANSTAAFL). Even simpler, when you were a kid, your parents told you not to take candy from strangers. The same applies to cryptocurrency.
Whether it’s a dusting attack, an ICO airdrop or a seemingly real post on Twitter that promises to give you free crypto if you take certain actions, if it looks too good to be true, then it usually is.
Just like with fiat currency, free crypto is almost never really “free”. There is always a price to pay.
On that note, let’s end with a good contemplation on dust, as done by Will Ferrell in “Old School”.
By Werner Vermaak
Disclaimer: CoolBitX does not endorse and is not responsible for or liable for any content, accuracy, quality or other materials on this page. Readers should do their own research before taking any actions.
CoolBitX is not responsible, directly or indirectly, for any damage or loss caused by or in connection with the use of or reliance on any content, goods or services mentioned in this guide.
Other Crypto Security Guides by CoolWallet:
Cryptojacking Guide

Phishing Guide